Email blacklist monitoring: checks and fixes for outreach domains
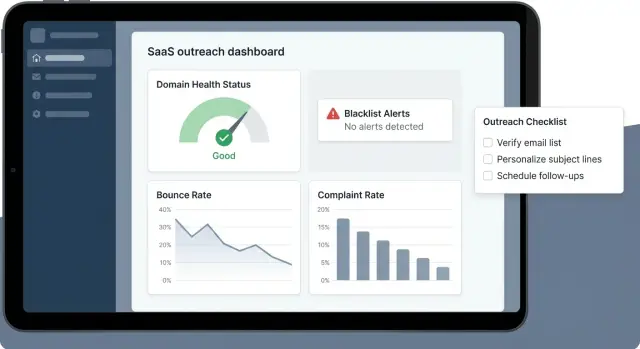
Email blacklist monitoring for outreach domains: where to check, which signals matter most, and a practical checklist to fix root causes and recover deliverability.
What blacklist monitoring is and why it matters for outreach
An email blacklist is a list maintained by spam-filter companies and mailbox providers that tracks sending sources tied to unwanted mail. If your domain, your sending IP, or both appear on one of these lists, your emails are more likely to land in spam, get blocked, or disappear without a clear error.
Outreach domains get listed more often than a main company domain because cold email creates risk by default: newer domains, faster volume ramps, and more recipients thinking, “Who is this?” Even if your message is legitimate, people can ignore it, mark it as spam, or unsubscribe. Those actions are strong negative signals, especially when they happen early and repeatedly.
It also matters what got flagged. A domain listing usually points to patterns tied to the domain name: content issues, authentication gaps, or poor list quality. An IP listing often points to sending behavior: sudden volume spikes, repeated bounces, or a weak reputation on that sending infrastructure. The fix can be different, so you want to identify the layer that’s actually taking the hit before you change anything.
Blacklist monitoring works best as an early-warning system. The goal isn’t to panic over one alert. It’s to catch trouble while it’s still small, confirm whether it’s affecting inbox placement, and adjust the underlying cause.
A solid monitoring setup helps you:
- Catch new listings early and verify whether inbox placement changed.
- Separate domain issues from IP issues.
- Spot rising complaints, bounces, and unsubscribes before filters tighten.
- Keep authentication and sending habits consistent as volume grows.
- Decide when to pause, adjust, or keep sending.
Domain, mailbox, and IP reputation: the basics you need
Outreach deliverability is usually judged in three layers: domain, mailbox, and IP. Mixing them up leads to wasted effort, because you end up treating symptoms instead of the cause.
Domain reputation is trust tied to your sending domain (the part after the @). It builds from consistent, wanted sending over time. If a domain becomes associated with spam-like behavior, every mailbox on that domain can feel it.
Mailbox reputation is narrower: the history of one sender address (like [email protected]). Mailbox-level problems often come from that one account: high bounces, too many complaints, or sending patterns that look automated. Mailbox issues can spill over, though. If several mailboxes on the same domain perform poorly, the domain itself starts to look risky.
IP reputation is trust tied to the server IP that sends your emails. Some setups rely on shared sending IPs, while others isolate infrastructure per customer or team. If the IP is flagged, even a well-behaved domain can see inbox placement drop until the IP recovers.
New domains and new mailboxes are fragile because they don’t have a track record. A jump from 0 to 500 emails a day, messy lists, or sending to many unknown addresses can trigger filters quickly.
When you see deliverability trouble, start with a few simple questions:
- Which layer is affected: domain, mailbox, or IP?
- Is it one sender or several?
- Did volume, targeting, or copy change in the last week?
- Are bounces or complaints rising?
Infrastructure choices can limit the blast radius. For example, LeadTrain uses tenant-isolated sending infrastructure via AWS SES, which helps prevent another organization’s behavior from dragging down your IP reputation. Isolation helps, but your own list quality and sending patterns still matter most.
Where to check: the main places issues show up
Problems rarely begin with a single blacklist alert. Early warnings usually appear in the same few places, and blacklist status is only one input.
DNS-based blacklists (DNSBLs)
A DNSBL “hit” means a list has associated your sending IP (and sometimes your domain) with unwanted mail. Some lists are strict and meaningful; others are noisy. One hit might not change inboxing, but multiple hits, or a hit on widely used lists, often lines up with real deliverability issues.
Mailbox provider signals (what actually moves inbox placement)
Mailbox providers don’t “trust” you just because you aren’t listed somewhere. They watch recipient behavior: spam complaints, engagement drops, and provider-specific blocks. If Gmail or Microsoft starts throttling, that usually matters more than a minor DNSBL mention.
A practical monitoring set usually includes:
- DNSBL lookups for your sending IPs and domains (and whether a hit is new).
- Provider dashboards such as Google Postmaster Tools and Microsoft SNDS (when available).
- Sending logs for blocks, throttling, and deferrals.
- Bounce reports grouped by reason, not just “bounced.”
- Authentication results (pass/fail and alignment).
Bounce data is one of the clearest signals because it’s specific:
- Hard bounce: address doesn’t exist (list quality problem).
- Soft bounce: temporary issue (full inbox, rate limiting, timing).
- Block/policy rejection: provider refused you (treat as urgent).
Also confirm authentication outcomes. You want SPF and DKIM to pass, and DMARC alignment to be correct (the visible From domain should match what SPF/DKIM authenticate). If alignment fails, providers may still accept the mail, but trust it less, and complaints tend to hurt more.
Signals that matter more than a single blacklist hit
A blacklist alert is worth attention, but it’s rarely the whole story. Monitoring works best when you watch patterns that show whether providers are losing trust.
Rising hard bounces are one of the clearest red flags. A few bounces are normal, but a jump often means stale data, a weak list source, or mailing domains that reject unknown senders.
Spam complaint rate matters even more. Complaints often spike right after a change: a faster ramp, a new list import, or messaging that feels misleading. Even small increases are meaningful because the signal comes from real people clicking “This is spam.”
A sudden drop in opens or replies can also be an early warning sign, especially if targeting and offer didn’t change. It can mean your emails started landing in spam, moved to a less visible tab, or are being rate-limited quietly.
Watch closely for bounce reasons that include “message blocked” or “policy rejection.” Those aren’t normal inbox-full errors. They usually point to missing or misaligned authentication, suspicious link patterns, sending behavior that looks automated, or a domain that’s too new for the volume you’re pushing.
If you want a simple triage set, track these together:
- Hard bounces rising week over week
- Complaints appearing right after a campaign edit
- Opens dropping across multiple providers
- “Blocked” or “policy” bounces increasing
- Unsubscribes spiking on the first email
Example: if you add 5,000 new prospects and hard bounces double while policy rejections appear, the root cause is usually list quality plus a volume jump, not “a blacklist problem.”
Authentication checks: SPF, DKIM, DMARC without jargon
If you do only one technical step as part of monitoring, make it this: confirm your domain authentication is correct. These records don’t guarantee inbox placement, but broken or misaligned authentication is a fast way to lose trust.
SPF: “Am I allowed to send from this domain?”
SPF is a public list of which services are allowed to send mail for your domain. Common problems are basic: multiple SPF records, forgetting to include a new sending service, or creating a record that fails due to hidden complexity.
Quick SPF checks:
- Exactly one SPF TXT record exists for the domain.
- It includes the service that actually sends your outreach.
- It ends with a clear policy (often
~allwhile testing, later sometimes-all). - It doesn’t fail because of too many DNS lookups.
- It’s published on the correct domain (many teams send from a subdomain but edit the root).
DKIM: “Can the receiver verify the message wasn’t tampered with?”
DKIM adds a signature to each email. If the signature is missing or fails, providers have less reason to trust your mail.
Typical failure points: the DKIM record was never published, the sender is using the wrong DKIM selector, or a mailbox/provider change happened and the old DKIM setup was left behind.
DMARC and alignment: “Do these checks match the domain people see?”
DMARC ties everything together and adds a policy. Start in monitoring mode (p=none) so you can observe without blocking good mail. Tighten gradually once results are consistently clean.
The part many teams miss is alignment. An email can “pass SPF” or “pass DKIM,” but still fail DMARC if those passes apply to a different domain than the one in the visible From address. For outreach, that mismatch hurts trust.
A practical approach: publish DMARC in monitoring mode, confirm alignment for your exact From domain (and any subdomain you send from), then move to quarantine/reject only after you see stable results.
Step by step: a simple monitoring routine you can follow
Start with a clear sending identity. Decide what you’re protecting: one outreach domain with a few mailboxes, or several domains with one mailbox each. Either can work, but consistency makes your data easier to interpret.
Set a safe ramp-up schedule before you send anything important. The goal is steady, predictable volume. When you add a new mailbox, treat it like a new sender even if the domain is older. Keep sending days and hours consistent so you don’t create sudden spikes.
Warm-up helps, but it won’t fix bad targeting, spam complaints, or broken authentication.
A simple weekly routine that stays manageable:
- Track sending volume per mailbox and flag spikes.
- Review bounce rate and top bounce reasons.
- Watch complaint and unsubscribe rates for sudden changes.
- Monitor engagement trends (opens/replies) and inbox-to-spam shifts.
- Re-check SPF/DKIM/DMARC after any DNS, domain, or sending change.
Once a month, do a deeper review. Check domain and IP status where you typically see issues first: sending logs, provider blocks, and major reputation dashboards. If you find a blacklist hit, keep digging until you can name the cause (list quality, volume jump, new domain, broken authentication, or content/targeting mismatch).
Root causes: why outreach domains get into trouble
Most blacklist problems are symptoms. Monitoring helps you see the smoke, but the fire is usually one of four things: who you email, what you say, how fast you send, and what reputation your setup depends on.
Bad list quality is the fastest way to damage a new outreach domain. Old data drives bounces, and bounces tell providers you don’t maintain your list. Role accounts (info@, support@) and recycled addresses are also riskier, even if they look “valid.”
Complaints often come from mismatch, not “spammy words.” If the offer doesn’t fit the recipient’s role, industry, or timing, people hit spam because it’s the quickest way to stop the mail. Broad targeting and generic copy make this worse.
Cadence and volume are another common trigger. Big jumps in daily sends, or too many follow-ups too quickly, can cause filtering even without a blacklist listing.
Infrastructure matters because reputation can be shared. If you send through shared systems, someone else’s behavior can affect you.
Before you chase removals, do a quick root-cause check:
- Are bounces rising (old data, role accounts, weak segmentation)?
- Are complaints concentrated in one audience or one message?
- Did you change cadence, volume, or add a new sequence suddenly?
- Did you skip warm-up or start sending before authentication was stable?
Fixing these first is what prevents the same listings from coming back.
Common mistakes and traps that keep you stuck
The biggest trap is treating the blacklist as the problem. A listing is usually the signal, not the cause. If you rush to delist but keep sending the same way, you often get listed again.
Another common mistake is switching domains every time deliverability dips. It can feel like progress, but it often hides the real issue: weak targeting, scraped data, or poor hygiene. Constant rotation also makes it harder to build stable sender reputation.
Warm-up can become a distraction, too. It helps when the rest of your setup is healthy, but it can’t offset high bounce rates, rising complaints, or angry replies.
Many teams also over-index on opens. Opens can be noisy and misleading. Day to day, these tend to reveal the real issue faster:
- Hard bounces
- Spam complaint rate
- Unsubscribe rate (and how quickly you honor it)
- Reply quality (confusion and anger are signals)
- Sudden volume jumps
Response checklist: fix the cause before you ask for removal
A blacklist alert can feel urgent, but removal requests rarely stick if the underlying issue is still active. Treat it like a smoke alarm: stop the smoke first, then reset the alarm.
Start by limiting damage. If the spike came from a specific campaign, audience, or mailbox, pause that slice first instead of shutting everything down. Often it’s one bad import or one overly broad segment.
A root-cause checklist that’s usually effective:
- Reduce volume to the segment that triggered the issue (or pause it). Keep your best-performing segment running at a low, steady rate if it’s clean.
- Clean the list aggressively: remove hard bounces, obvious role accounts, and patterns that look scraped. If people never open after several attempts, stop mailing them.
- Keep identity consistent: the same From domain, aligned SPF/DKIM/DMARC, and no mid-sequence domain switching.
- Tighten the message: make intent clear in the first lines, narrow targeting, and cut extra links or heavy tracking if complaints are rising.
- Ramp back up only after bounce and complaint rates return to normal, then increase slowly over several days.
Two rules prevent most “quick fix” cycles:
- Don’t rotate to new domains as a shortcut. You’ll usually repeat the same mistake on a fresh reputation.
- Don’t keep sending “to test” while error rates are high. The test becomes the problem.
A realistic example: from blacklist alert to stable inboxing
A two-person outbound team launches a fresh outreach domain for a new offer. Week one looks fine: opens are decent, replies trickle in, and they ramp to 120 emails per day across three new mailboxes. In week two, bounces jump, replies slow down, and a few prospects say the emails are going to spam. A quick check shows the domain is listed on a minor blacklist, and one provider is issuing more temporary blocks.
They don’t start with removal requests. They look for the cause.
They pull three checks from sending logs: bounce types (hard vs. soft), any complaints, and which segments performed worst. Then they verify the basics: SPF/DKIM/DMARC pass on real sends, and the From address matches the authenticated domain. Finally, they review the list source. The worst bounces came from an older scraped segment that hadn’t been verified recently.
Same-day changes:
- Pause the risky segment and keep only recent, verified leads.
- Cut volume by about 60% and ramp back up slowly.
- Split campaigns by persona so the copy is more specific.
- Rewrite the first email to be shorter and more direct, with a clear opt-out line.
- Keep warm-up running so reputation doesn’t drop further.
Recovery isn’t instant. Over the next 2 to 4 weeks, they watch for fewer hard bounces, fewer temporary blocks, and more normal replies. The blacklist listing may clear earlier or later, but the real sign of progress is stable inbox placement and steady engagement as volume increases.
Next steps: keep it stable with simple habits
Most deliverability problems are repeatable and preventable. The point of monitoring is to catch small issues before they turn into a sending freeze.
Pick one day a week and check the same few signals: major blacklist status, bounce reasons, complaint and unsubscribe trends, and authentication health (SPF, DKIM, DMARC), especially after any DNS edit or new mailbox.
Write down a few thresholds ahead of time so you’re not making decisions under pressure:
- Pause new prospecting if bounces jump above your normal range for two days.
- Slow down if replies turn negative or unsubscribes spike.
- Investigate immediately if authentication breaks or a mailbox starts landing in spam.
- Ramp only after 3 to 5 clean days with stable bounces and normal replies.
Separating outreach from your main domain is another low-effort habit that prevents real damage. Keep your main business domain for customers, receipts, and important conversations, and use dedicated outreach domains for cold campaigns.
If you want fewer moving parts, using an all-in-one cold email platform like LeadTrain can help because domains, mailboxes, warm-up, sequences, and AI-powered reply classification live in one place. That makes it easier to spot what changed (volume, targeting, authentication, or reply mix) before a small issue becomes a deliverability problem.
FAQ
What is an email blacklist, and what happens if my outreach domain is on one?
An email blacklist is a database used by spam filters to flag domains or IPs associated with unwanted mail. If you’re listed, your outreach is more likely to be spam-foldered, blocked, or quietly throttled, even if your copy is fine.
Why do outreach domains get blacklisted more often than a company’s main domain?
Cold outreach domains are often newer, ramp volume faster, and message people who don’t recognize the sender yet. Early spam complaints, ignored emails, and bounces weigh more heavily when you don’t have an established sending history.
How do I tell if it’s a domain blacklist issue or an IP blacklist issue?
A domain listing usually points to problems tied to your domain identity, like authentication gaps, misalignment, or low-quality targeting that drives complaints. An IP listing more often points to sending behavior, like sudden volume spikes, repeated bounces, or poor reputation on the sending infrastructure.
I got a blacklist alert—should I stop all sending immediately?
Treat it as a signal, not an emergency. First confirm whether inbox placement changed using your sending logs and real mailbox checks, then look for what changed recently like list source, volume, cadence, or copy before you try to delist anything.
What signals matter more than a single blacklist hit?
Watch hard bounces, spam complaints, “blocked/policy” bounce reasons, and sudden drops in replies or opens across multiple providers. A single minor blacklist hit can be noise, but these trends usually mean providers are actively reducing trust.
What’s the simplest way to verify SPF, DKIM, and DMARC are actually helping deliverability?
You want SPF and DKIM to pass, and you want DMARC alignment so the visible From domain matches what SPF/DKIM authenticate. If alignment is wrong, providers may still accept mail but treat it as less trustworthy, so complaints and filtering get worse faster.
What’s a practical first-hour checklist when deliverability suddenly drops?
Start by pulling bounce and block reasons, then isolate whether it’s one mailbox, one segment, or all sending. Next, pause the risky slice, reduce volume, and fix the root cause like stale data, high complaints, or authentication issues before ramping again.
Does warm-up prevent blacklists, or is it overrated?
Warm-up helps you build a steady sending history, but it can’t compensate for bad lists, misleading targeting, or broken authentication. If bounces or complaints are high, warm-up won’t prevent filtering and may just prolong the damage.
Should I rotate to a new domain every time deliverability dips?
Constant domain switching hides the cause and resets your reputation back to zero, so you often recreate the same problem on a fresh domain. It’s usually better to slow down, clean your list, tighten targeting, and stabilize sending habits so the domain can recover.
How does LeadTrain’s tenant-isolated sending infrastructure affect blacklist risk?
It helps by reducing “blast radius,” since another customer’s behavior is less likely to harm your sending reputation. It doesn’t replace good practices, so you still need clean data, steady volume ramps, and aligned SPF/DKIM/DMARC to stay out of trouble.